Q. What’s the long term impact of an update gone bad?
A. Aversion to subsequent updates resulting in postponement of future updates for as long as possible.
Cumulative Updates for Microsoft Exchange Server 2013
 With Microsoft Exchange Server 2013, we’ve changed the way we deliver hotfixes and service packs. Instead of the priority-driven hotfix release and rollup update model used by previous versions of Microsoft Exchange, Exchange 2013 now follows a scheduled delivery model. In this model, cumulative updates (CU), which address customer-reported issues and may include new functionality and/or features, are released quarterly. Critical product updates, which are packages that address a Microsoft-released security bulletin or contain a change in time zone definitions, are released as needed on a monthly basis for the most recently released CU and the immediately previous CU.
With Microsoft Exchange Server 2013, we’ve changed the way we deliver hotfixes and service packs. Instead of the priority-driven hotfix release and rollup update model used by previous versions of Microsoft Exchange, Exchange 2013 now follows a scheduled delivery model. In this model, cumulative updates (CU), which address customer-reported issues and may include new functionality and/or features, are released quarterly. Critical product updates, which are packages that address a Microsoft-released security bulletin or contain a change in time zone definitions, are released as needed on a monthly basis for the most recently released CU and the immediately previous CU.
To get the latest version of Exchange 2013, download and install Microsoft Exchange Server 2013 Cumulative Update 14. Because each CU is a full installation of Exchange and includes updates and changes from all previous CU’s, you don’t need to install any previous CU’s or service packs first.
https://technet.microsoft.com/en-us/library/jj907309(v=exchg.150).aspx
Simple? Right?! Ha! Of course, if you’re reading this, you already know that.
Now, I’ll grant you. I walked into installation of Cumulative Update 14 in an effort to help resolve problems with an installation of an On Premises Exchange Server 2013 that had suddenly, and recently, begin having problems with OWA. So, there was already a problem before this. That said, the problems I encountered during this installation, which was a jump from Exchange Server 2013 Cumulative Update 7 (which had completed without a hitch) on a Hyper-V Guest on Windows Server 2012, could have been entirely addressed by better error handling when Microsoft prepped the CU – which would have saved my customer – and a lot of other people’s, too – a ton of money, and me a few hours of sleep. Many thanks to those in the forum and blogospheres for helping me solve this problem.
A couple of brief notes :
- First, if you’re reading this, you are an IT Admin – no other reason to read this.
- Second, you’re probably in crisis mode – so find your error and hit the solutions so you can move onto other fires.
- Third, you’ve probably already rebooted a number of times after attempting various solutions – be prepared for one or two more.
- Finally, and I cannot stress this enough, slow down. Seriously. Take a breath, and plan for this to take 2-3 hours, depending on infrastructure and replication time. Plan on coffee breaks and/or naps.
Prequisite Steps
- Make sure you have backups.
- Disable the Security Software on your Exchange Server until this is all complete.
Setup Errors
ServiceControl.ps1 cannot be loaded because you opted not to run this software now
Error:
The following error was generated when “$error.Clear();
& $RoleBinPath\ServiceControl.ps1 Save
” was run: “System.Management.Automation.PSSecurityException: File C:\Windows\Temp\ExchangeSetup\ServiceControl.ps1 cannot be loaded because you opted not to run this software now. —> System.UnauthorizedAccessException: File C:\Windows\Temp\ExchangeSetup\ServiceControl.ps1 cannot be loaded because you opted not to run this software now.
— End of inner exception stack trace —
at System.Management.Automation.AuthorizationManager.ShouldRunInternal(CommandInfo commandInfo, CommandOrigin origin, PSHost host)
at System.Management.Automation.CommandDiscovery.ShouldRun(ExecutionContext context, PSHost host, CommandInfo commandInfo, CommandOrigin commandOrigin)
at System.Management.Automation.CommandDiscovery.LookupCommandProcessor(CommandInfo commandInfo, CommandOrigin commandOrigin, Nullable`1 useLocalScope, SessionStateInternal sessionState)
at System.Management.Automation.CommandDiscovery.LookupCommandProcessor(String commandName, CommandOrigin commandOrigin, Nullable`1 useLocalScope)
at System.Management.Automation.ExecutionContext.CreateCommand(String command, Boolean dotSource)
at System.Management.Automation.PipelineOps.AddCommand(PipelineProcessor pipe, CommandParameterInternal[] commandElements, CommandBaseAst commandBaseAst, CommandRedirection[] redirections, ExecutionContext context)
at System.Management.Automation.PipelineOps.InvokePipeline(Object input, Boolean ignoreInput, CommandParameterInternal[][] pipeElements, CommandBaseAst[] pipeElementAsts, CommandRedirection[][] commandRedirections, FunctionContext funcContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6.Run(InterpretedFrame frame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(InterpretedFrame frame)”.
Solution
- Admin Powershell
- C:\Windows\Temp\ExchangeSetup\ServiceControl.ps1
- Answer [A] for “Always Run”
credit : https://support.microsoft.com/en-us/kb/2034420
The Active Directory schema isn’t up-to-date, and this user account isn’t a member of the ‘Schema Admins’ and/or ‘Enterprise Admins’ groups
Welcome to Microsoft Exchange Server 2013 Cumulative Update 14 Unattended Setup
Copying Files…
File copy complete. Setup will now collect additional information needed for
installation.
Performing Microsoft Exchange Server Prerequisite Check
Prerequisite Analysis FAILED
The Active Directory schema isn’t up-to-date, and this user account isn’t a
member of the ‘Schema Admins’ and/or ‘Enterprise Admins’ groups.
For more information, visit: http://technet.microsoft.com/library(EXCHG.150
)/ms.exch.setupreadiness.SchemaUpdateRequired.aspx
Setup encountered a problem while validating the state of Active Directory:
Active Directory operation failed on thalamus.mdtclinics-sw.local. This error c
ould have been caused by user input or by the Active Directory server being unav
ailable. Please retry at a later time. Additional information: Active directory
response: The operation was aborted because the client side timeout limit was ex
ceeded. . See the Exchange setup log for more information on this error.
For more information, visit: http://technet.microsoft.com/library(EXCHG.150
)/ms.exch.setupreadiness.AdInitErrorRule.aspx
The forest functional level of the current Active Directory forest is not W
indows Server 2003 native or later. To install Exchange Server 2013, the forest
functional level must be at least Windows Server 2003 native.
For more information, visit: http://technet.microsoft.com/library(EXCHG.150
)/ms.exch.setupreadiness.ForestLevelNotWin2003Native.aspx
A Setup failure previously occurred while installing the PreSetup role. Eit
her run Setup again for just this role, or remove the role using Control Panel.
For more information, visit: http://technet.microsoft.com/library(EXCHG.150
)/ms.exch.setupreadiness.InstallWatermark.aspx
Either Active Directory doesn’t exist, or it can’t be contacted.
For more information, visit: http://technet.microsoft.com/library(EXCHG.150
)/ms.exch.setupreadiness.CannotAccessAD.aspx
The Exchange Server setup operation didn’t complete. More details can be found
in ExchangeSetup.log located in the :\ExchangeSetupLogs folder.
Solution Part 1
30 minutes or more, depending on replication time.
- Login to the DC (not the Exchange Server)
- Open Active Directory Domains and Trusts
- Right click your domain
- Choose Raise Domain Functional Level
- Verify that Current domain functional level is at least Server 2003
- Raise it on each DC to 2003.
- What IS the current Domain Functional Level?
- Click Cancel if there are no changes
- Repeat on additional Domain Controllers
- Right click “Active Directory Domains and Trusts
- Click Raise Forest functional level
- Verify that the Current forest functional level is at least 2003 AND that it is the same as your Domain functional level
- If necessary, Raise the functional level to the same as your lowest allowable domain functional level.
- Click Cancel if there are no changes
- Open Active Directory Users and Computers
- Check your user account’s Group Membership
- Verify the following :
- Member of “Enterprise Admins”
- Member of “Schema Admins”
- Primary Group Membership is an Admin membership group
- REMOVE account membership in Domain Users group.
- Admin PowerShell (on the primary DC)
- Navigate to the path of your extracted setup.exe for the CU
- [full path]\setup.exe /PrepareSchema /IAcceptExchangeServerLicenseTerms
Credit : Paul Cunningham : http://exchangeserverpro.com/exchange-2013-installing-cumulative-updates/
Credit : cdoctor Users group comment : https://social.technet.microsoft.com/Forums/Sharepoint/en-US/41256f43-8040-4fe2-ae73-4754f4ca7815/unable-to-install-exchange-2013-on-server-2012-server?forum=exchangesvrdeploy
Welcome to Microsoft Exchange Server 2013 Cumulative Update 14 Unattended Setup
Copying Files…
File copy complete. Setup will now collect additional information needed for installation.
Performing Microsoft Exchange Server Prerequisite Check
Prerequisite Analysis COMPLETED
Configuring Microsoft Exchange Server
Extending Active Directory schema COMPLETED
The Exchange Server setup operation completed successfully.
Solution Part 2
2 Hours to Complete
- Logon to the server running Exchange
- Admin PowerShell
- navigate to location of extracted CU files
- [full path]\setup.exe /m:upgrade /IAcceptExchangeServerLicenseTerms
- IF you still get the error, once again, double check the logged on account and verify that it is NOT a member of the Domain Users Group
- CU setup checks to see if the account is a member of Users. If it is a member of the Domain Users group, it assumes that the account is NOT a member of Enterprise Admin and Schema Admins, even when it is, resulting in the erroneous error. The reasons aren’t important – just change the Primary Group membership to something else, like Domain Admins, and remove your account’s membership in Domain Users, then repeat Step 4.
- In some cases, after changing group memberships, you’ll have to logoff, and then repeat Solution Part 2.
- Reboot the Exchange Server
Welcome to Microsoft Exchange Server 2013 Cumulative Update 14 Unattended Setup
Copying Files…
File copy complete. Setup will now collect additional information needed for installation.
Languages
Mailbox role: Transport service
Client Access role: Front End Transport service
Mailbox role: Client Access service
Mailbox role: Unified Messaging service
Mailbox role: Mailbox service
Management tools
Client Access role: Client Access Front End service
Performing Microsoft Exchange Server Prerequisite Check
Configuring Prerequisites COMPLETED
Prerequisite Analysis COMPLETED
Configuring Microsoft Exchange Server
Preparing Setup COMPLETED
Stopping Services COMPLETED
Language Files COMPLETED
Removing Exchange Files COMPLETED
Preparing Files COMPLETED
Copying Exchange Files COMPLETED
Language Files COMPLETED
Restoring Services COMPLETED
Language Configuration COMPLETED
Mailbox role: Transport service COMPLETED
Client Access role: Front End Transport service COMPLETED
Mailbox role: Client Access service COMPLETED
Mailbox role: Unified Messaging service COMPLETED
Mailbox role: Mailbox service COMPLETED
Exchange Management Tools COMPLETED
Client Access role: Client Access Front End service COMPLETED
Finalizing Setup COMPLETED
The Exchange Server setup operation completed successfully.
Mailbox server role isn’t installed on this computer
I would periodically encounter this message after a failed attempt at installing the CU.
Solution
Reboot the Exchange Server, verify the steps from the top of this post are all followed and you shouldn’t see this message again.
Post Install Steps
I’m only adding this as a reminder, because, odds are, it’s late at night or the wee hours of the morning and you’re sleep deprived:
- Re-enable Security Software
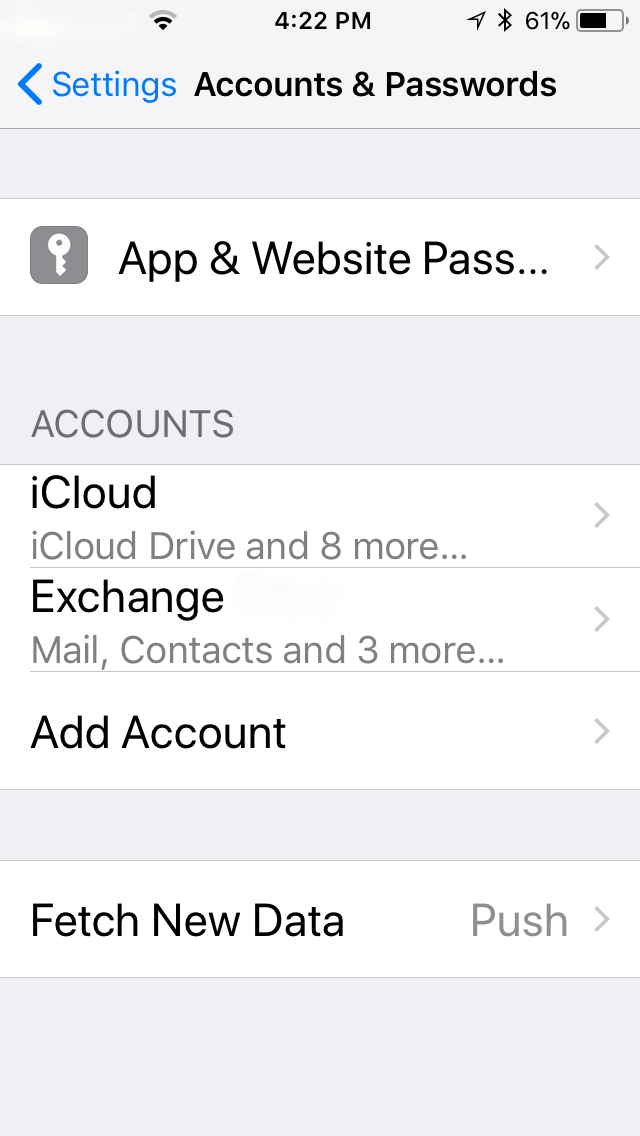
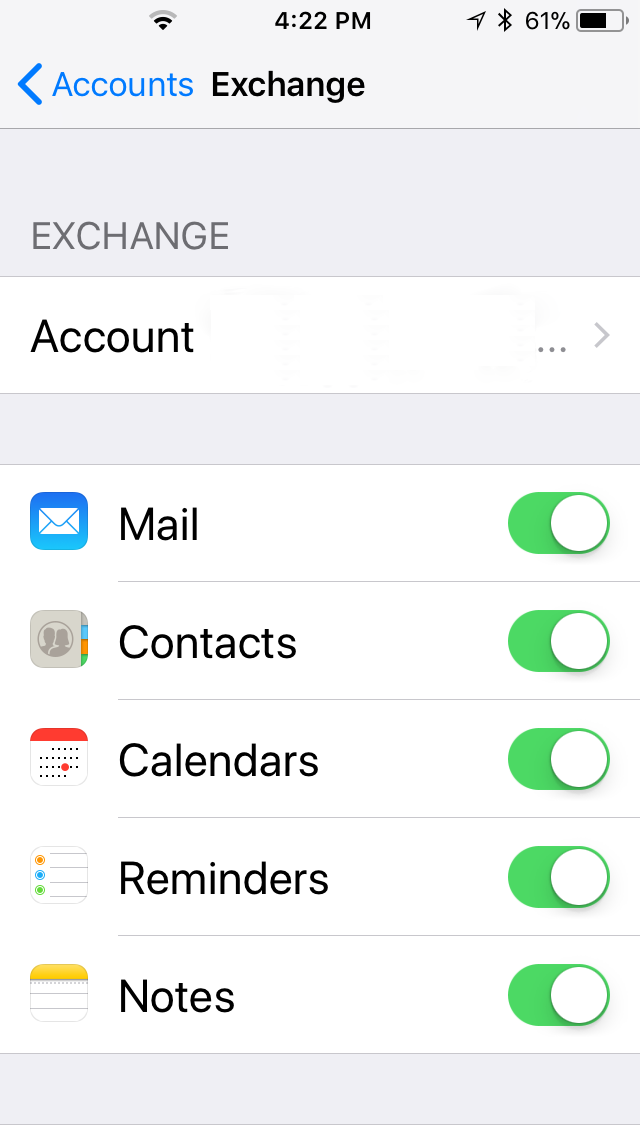
- Verify functionality of :
With any luck, it didn’t cost you a full day just to get here. For me, this was a two day ordeal, especially since each attempt plus server restart costs a good 20-40 minutes. I read some commenters say it took them three days to get their CU installed successfully. No server patch installation should be this much of a nightmare.
A couple more resources :
- This article mentions the use of Mark Russinovich’s Streams tool to remove the streams flags from the downloaded, extracted CU install files. In my case, it made no difference, but it saved some people
- This is a pretty good writeup, just pay attention to his update and remember not to use the shortcuts. Issue #6 was one that I ran into because I failed to use a full path to the CU setup.exe :
- I listed this earlier, but, when you’re not in crisis mode, do take a 15 minutes and read through Paul Cunningham’s “Installing Cumulative Updates and Service Packs for Exchange Server 2013.” It is comprehensive, and explains a lot.
- http://exchangeserverpro.com/exchange-2013-installing-cumulative-updates/
Good luck!

 With Microsoft Exchange Server 2013, we’ve changed the way we deliver hotfixes and service packs. Instead of the priority-driven hotfix release and rollup update model used by previous versions of Microsoft Exchange, Exchange 2013 now follows a scheduled delivery model. In this model, cumulative updates (CU), which address customer-reported issues and may include new functionality and/or features, are released quarterly. Critical product updates, which are packages that address a Microsoft-released security bulletin or contain a change in time zone definitions, are released as needed on a monthly basis for the most recently released CU and the immediately previous CU.
With Microsoft Exchange Server 2013, we’ve changed the way we deliver hotfixes and service packs. Instead of the priority-driven hotfix release and rollup update model used by previous versions of Microsoft Exchange, Exchange 2013 now follows a scheduled delivery model. In this model, cumulative updates (CU), which address customer-reported issues and may include new functionality and/or features, are released quarterly. Critical product updates, which are packages that address a Microsoft-released security bulletin or contain a change in time zone definitions, are released as needed on a monthly basis for the most recently released CU and the immediately previous CU. On a recent morning I logged into my online bank account and noticed the following message :
On a recent morning I logged into my online bank account and noticed the following message : You are driving to work, and it is your day to carpool. You drive your 4 door sedan and pick up 4 people. While on your drive to work you find out that your car needs to be updated to fix a major security problem. Seems someone can remotely turn on your turn signal without you knowing about it, making you the person driving down the road for 30 minutes without changing lanes or turning. Well, you certainly don’t want that so, when you reach work and park your car, you push the update button and walk into work with your car pool buddies. At the end of the day, though, your whole crew comes out of the office, ready to go home and discover that the update has also changed your 4 door sedan into a 2 door sports coupe. Sure, the blinker can’t be turned on remotely, anymore, but, seriously?!
You are driving to work, and it is your day to carpool. You drive your 4 door sedan and pick up 4 people. While on your drive to work you find out that your car needs to be updated to fix a major security problem. Seems someone can remotely turn on your turn signal without you knowing about it, making you the person driving down the road for 30 minutes without changing lanes or turning. Well, you certainly don’t want that so, when you reach work and park your car, you push the update button and walk into work with your car pool buddies. At the end of the day, though, your whole crew comes out of the office, ready to go home and discover that the update has also changed your 4 door sedan into a 2 door sports coupe. Sure, the blinker can’t be turned on remotely, anymore, but, seriously?!